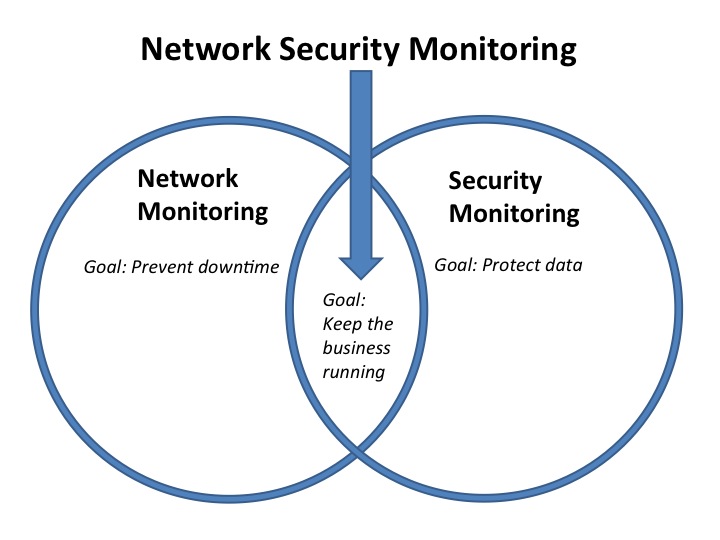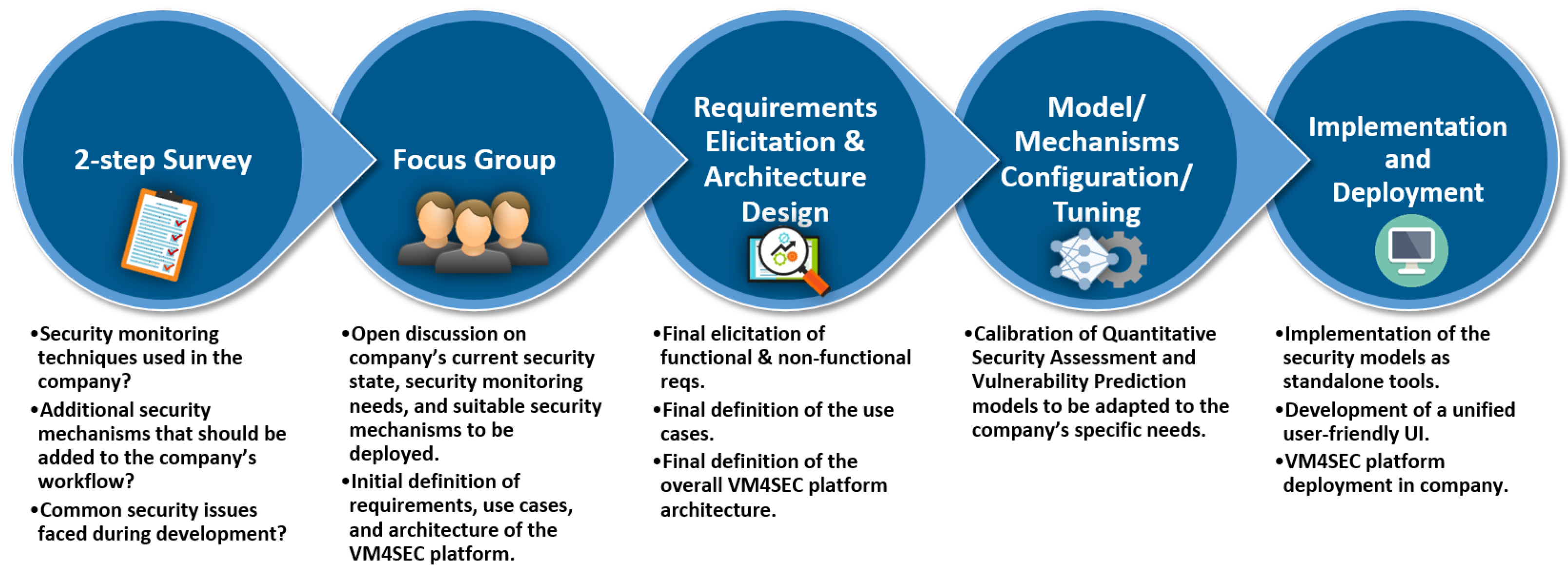
Applied Sciences | Free Full-Text | Security Monitoring during Software Development: An Industrial Case Study
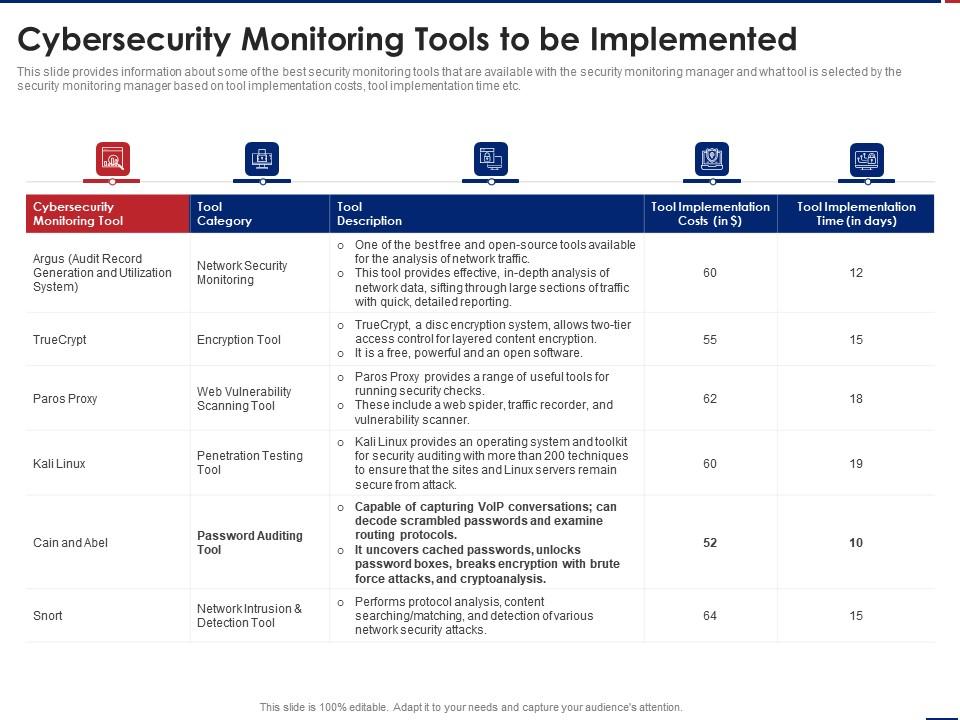
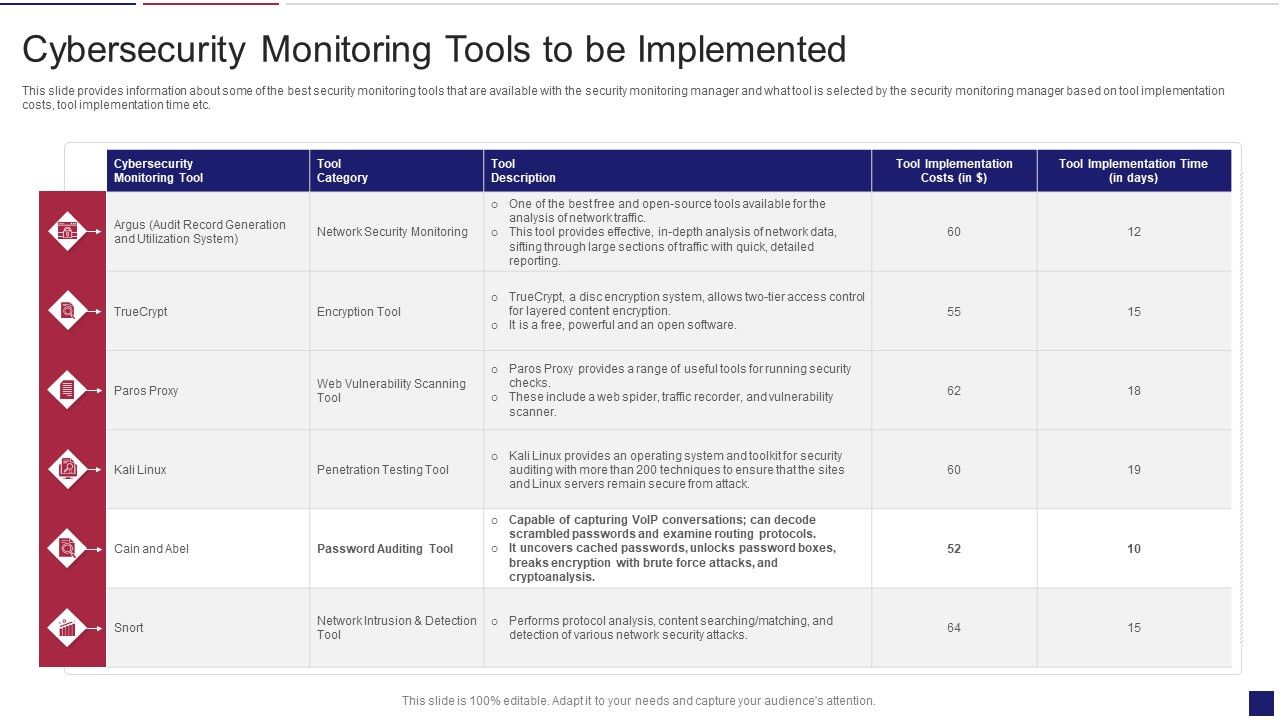
Effective Security Monitoring Plan Cybersecurity Monitoring Implemented Ppt Example | Presentation Graphics | Presentation PowerPoint Example | Slide Templates